New malware that steals bank data threatens Android users
Android malware known as FluBot is continuing to cause mayhem across some European countries, and there is speculation that the threat actors behind it may decide to target other geographies, including the United States.

A banking trojan called FluBot, which has attacked several Android users in Spain and other European countries, threatens to reach more areas of the planet soon, mainly the United States and Latin America. The alert was given on Tuesday (25) by the information security company ESET.
According to the company, the malware reaches mobile phones through a campaign that includes sending SMS on behalf of a logistics company such as DHL, FedEx or UPS, for example. In the message, the victim is asked to install a supposed branded app, with the malicious file embedded.
Installed on the device, FluBot is able to steal credit card numbers and bank access credentials, as well as capture data typed on the screen and release spam and spyware. It can also extract the contact list and make it available to the hackers who command the scam, allowing them to reach potential new victims.
How FluBot operates
If a victim is lured by the attacker into the malicious campaign, their entire Android device becomes accessible to the scammer. This includes the potential to steal credit card numbers and access credentials to online banking accounts. To avoid removal, the attacker implements mechanisms to stop the built-in protection offered by the Android OS and stops many third-party security software packages from being installed, an action many users would take to remove malicious software.
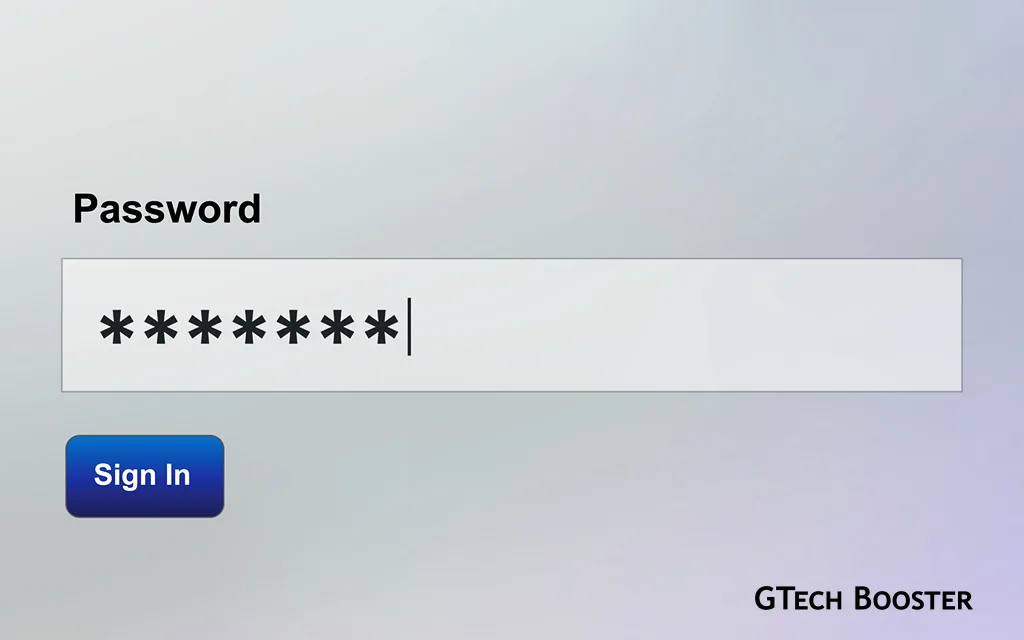
The victim first receives an SMS message that impersonates a popular delivery logistics brand, such as FedEx, DHL, and Correos (in Spain). The call to action of the message is for the user to click a link in order to download and install an app that has the same familiar branding as the SMS message but is actually malicious and has the FluBot malware embedded within it. An example of the SMS message (in German) and the subsequent prompt to install the app can be seen below:

How to remove FluBot
A compromised device may need to have the malware removed manually. You may follow the video below for guidance.
Whether this malware makes it to other continents in any significant number or not, the functionality and the devastation already caused in Europe should heighten the call to action for all Android users; to watch out for suspicious messages and to install security software in order to prevent such extremely malicious apps from ever getting on their devices.