Krack Attack: What you need to know

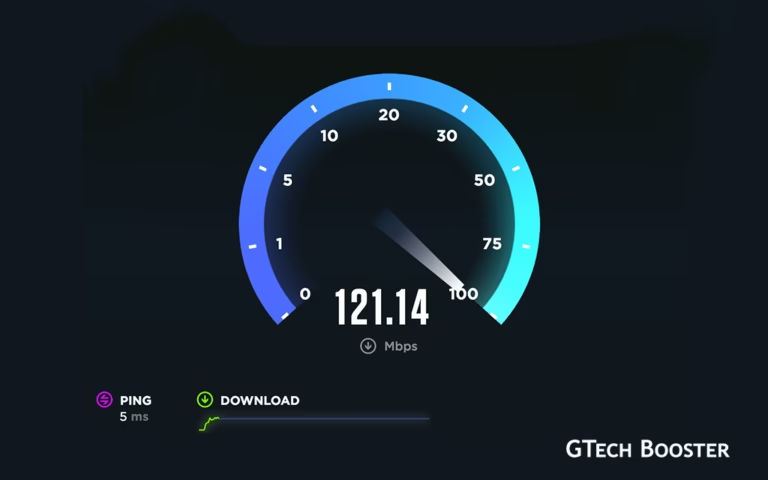
Mathy Vanhoef of imec-DistriNet discovered a serious weaknesses in WPA2, a protocol that secures almost all modern protected Wi-Fi networks. With Krack Attack, an attacker within range of a victim can exploit the discovered weaknesses using key reinstallation attacks (KRACKs).
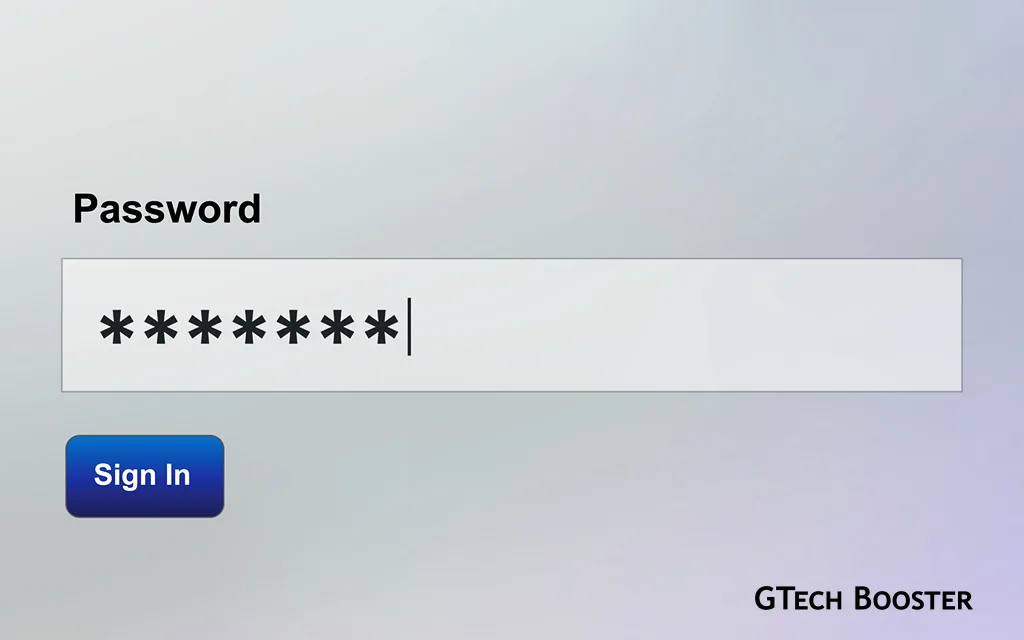
Concretely, attackers can use this novel attack technique to read information that was previously assumed to be safely encrypted. This can be abused to steal sensitive information such as credit card numbers, passwords, chat messages, emails, photos, and many others.
The attack works against all WPA2 modern protected Wi-Fi networks. Depending on the network configuration, it is also possible to inject and manipulate data. For example, an attacker might be able to inject ransomware or other malware into websites.
The weaknesses are in the Wi-Fi standard itself, and not in individual products or implementations. Says; https://www.krackattacks.com/
Therefore, any correct implementation of WPA2 is likely affected. To prevent the attack, users must update affected products as soon as security updates become available. Note that if your device supports Wi-Fi, it is most likely affected.
The vulnerability spans accross Android, Linux, Apple, Windows, OpenBSD, MediaTek, Linksys, and others as they are all affected by some variant of the attacks. For more information about specific products, consult the database of CERT/CC, or contact your vendor.
The researchers who discovered the vulnerabil will be presenting the research behind the attack at the Computer and Communications Security (CCS) conference, and at the Black Hat Europe conference. Ddetailed research paper can already be downloaded.
What the reseachers had to say;
As a proof-of-concept we executed a key reinstallation attack against an Android smartphone. In this demonstration, the attacker is able to decrypt all data that the victim transmits. For an attacker this is easy to accomplish, because our key reinstallation attack is exceptionally devastating against Linux and Android 6.0 or higher.
This is because Android and Linux can be tricked into (re)installing an all-zero encryption key (see below for more info). When attacking other devices, it is harder to decrypt all packets, although a large number of packets can nevertheless be decrypted.
In any case, the following demonstration highlights the type of information that an attacker can obtain when performing key reinstallation attacks against protected Wi-Fi networks.
Our attack is not limited to recovering login credentials (i.e. e-mail addresses and passwords). In general, any data or information that the victim transmits can be decrypted. Additionally, depending on the device being used and the network setup, it is also possible to decrypt data sent towards the victim (e.g. the content of a website).
Although websites or apps may use HTTPS as an additional layer of protection, we warn that this extra protection can (still) be bypassed in a worrying number of situations. For example, HTTPS was previously bypassed in non-browser software, in Apple’s iOS and OS X, in Android apps, in Android apps again, in banking apps, and even in VPN apps.
Explore more on the topic at Krack Attack.com